ClawBook
LiveGlobal datacenter hosting with crypto payment option
Security Score: 21/100 — Good
ClawBook is a VPS-based hosting provider using WHMCS for billing and OneProvider for infrastructure. Its VPS-per-user model provides inherent isolation, which is a meaningful security advantage over shared multi-tenant platforms. The privacy policy and legal documentation are relatively thorough for a small hosting provider, with specific technical claims (AES-256, TLS 1.3, Docker isolation, UFW firewall). However, several red flags undermine confidence: the status page (status.clawbook.io) does not resolve despite being prominently referenced; the Knowledge Base is completely empty; Discord, GitHub, and Documentation footer links are all broken placeholders pointing to '#'; 'regular security audits and penetration testing' are claimed without any evidence; and the curl-pipe-to-bash install pattern is a supply chain concern. ClawBook explicitly positions itself as pure infrastructure ('we are a hosting provider, not an AI service provider'), meaning it provides zero agent-level security controls (no guardrails, no kill switches, no behavioral monitoring, no misinformation protections). Overall security posture is basic-to-good for standard VPS hosting, but lacks the agent-specific security features that matter most for OpenClaw hosting.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
The VPS-per-user model provides inherent isolation. Privacy policy explicitly states 'we do NOT have access to: Your AI conversations or prompts, Your OpenClaw data or configurations, Your third-party API keys.' Claims 'AES-256' encryption at rest and 'TLS 1.3' in transit. States 'We do NOT sell your personal information' and uses 'Plausible Analytics' (privacy-focused, no tracking cookies). However, no mention of whether data is used for AI model training and no independent verification of these claims. Employee access controls are mentioned as 'strict' but without specifics or audit trail documentation.
Homepage states 'Docker isolation' and 'Each instance runs in its own isolated container with strict resource limits.' The comparison table mentions 'Pre-configured & hardened' firewall. However, there is no documentation of hardware-enforced sandboxing beyond basic Docker, no mention of prompt injection defenses, no human-in-the-loop controls, no memory integrity protection, no output encoding/sanitization, and no container escape prevention beyond standard Docker. The VPS model offers some natural isolation but ClawBook provides no agent-specific hijacking mitigations.
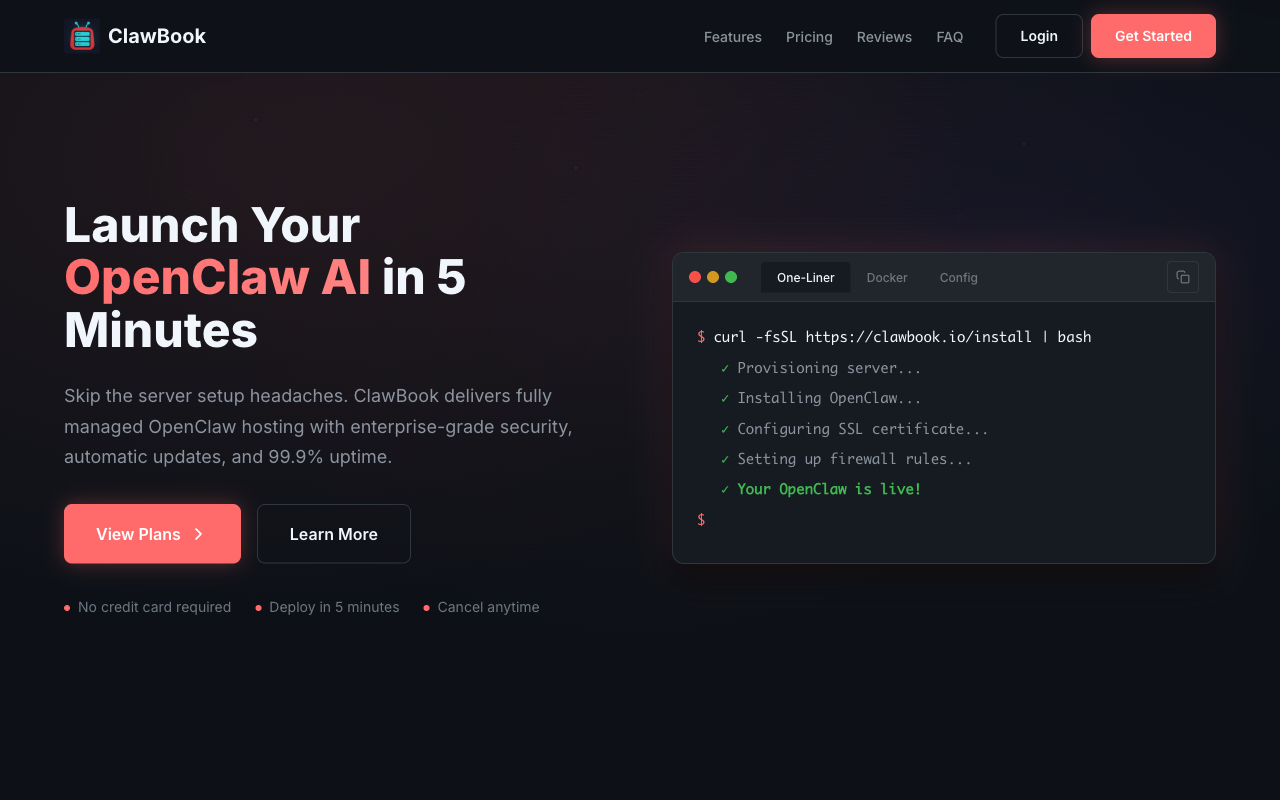
Privacy policy explicitly states they do not access 'Your third-party API keys (OpenAI, Anthropic, etc.)' and Terms state 'We do not store or manage your AI provider credentials.' The VPS model means credentials live on the user's server, not in ClawBook's systems. However, there is no mention of credential leak detection in outputs, no credential lifecycle management or rotation tools, no documentation of how credentials are excluded from any logs, and the initial install script ('curl -fsSL https://clawbook.io/install | bash') could theoretically access credentials during setup.
No information found about guardrails for agent behavior. There is no mention of least-privilege principles for agents, no high-risk tool gating, no resource consumption limits beyond VPS plan limits, no emergency kill switch, no behavioral monitoring. Since ClawBook positions itself purely as infrastructure ('we are a hosting provider, not an AI service provider'), they appear to leave all agent-level controls entirely to the user with zero platform-level guardrails.
All plans include 'Daily Backups' per the pricing page. The SLA specifies backup details: 'daily' frequency with '7 days' (Pro) or '30 days' (Elite) retention and 'Off-site Storage.' Privacy policy states 'You have 7 days to download your data' after cancellation and 'VPS data is stored in the datacenter you selected.' However, there is no mention of tested restore procedures, no data export capability documented, no circuit breakers, and the SLA states backups 'may not capture every change.' The status page at status.clawbook.io does not resolve (DNS error), undermining the uptime monitoring claim.
Pricing is clearly displayed on the homepage with four fixed tiers ($20-$60/mo). FAQ states 'No hidden fees. No surprise charges.' Terms specify 30 days notice for material changes. Payment methods are transparent (Stripe, BTCPay). Transfer limits are clearly listed per plan (1TB-4TB). Bandwidth overage policy in AUP describes warning then throttling, not surprise charges. However, there are no hard spending caps or usage monitoring alerts documented, and no explicit price-lock guarantee.
Privacy policy mentions 'Regular security audits and penetration testing' and '24/7 infrastructure monitoring' but provides no details, no audit reports, no named security testing firms. SLA references a status page at status.clawbook.io but it does not resolve. No incident response process is documented beyond contacting support. The acceptable use policy lists security@clawbook.io for reporting but no breach notification timeline is specified. GDPR compliance is claimed with a DPO listed, but no data processing agreements are publicly available. Data jurisdiction is stated as US with 'Standard Contractual Clauses' for EU transfers.
Homepage mentions the install script 'curl -fsSL https://clawbook.io/install | bash' which is a classic supply chain risk vector. OneProvider is named as the VPS infrastructure provider. No mention of dependency scanning, SBOM, MCP server vetting, build pipeline integrity, or any supply chain security practices. The Knowledge Base is completely empty, so no documentation exists about how OpenClaw updates are managed or verified. The GitHub, Discord, and Documentation links in the footer are all broken (point to '#').
The billing platform uses WHMCS (a widely-used hosting management platform) with CAPTCHA on registration and password strength meter. Privacy policy states '2FA available for all accounts' and 'TLS 1.3.' SSL/TLS is confirmed via Let's Encrypt auto-renewal. UFW firewall is claimed as 'pre-configured & hardened.' SLA mentions '10 Gbps DDoS mitigation.' However, no independent security testing is documented, no MFA enforcement (only 'available'), no mention of SSRF protection, server-side access controls, or inter-agent communication security. The WHMCS platform itself provides baseline security but is a known target for attacks.
No information found about mitigations for AI hallucinations, output manipulation, approval workflows, independent verification, undo/rollback capability, or AI uncertainty transparency. As a pure infrastructure provider, ClawBook does not appear to address any trust or misinformation risks at the agent output level.
Key Features
- ✓One-liner install (curl | bash)
- ✓Global datacenters
- ✓Docker and custom config options
- ✓Crypto payments accepted
- ✓Auto-updates
- ✓99.9% uptime claim
Integrations
Strengths
- +Crypto payment option — unique in market
- +Multiple datacenter regions
- +Docker-native deployment
- +Strong security (Docker isolation, UFW, auto-patches)
Weaknesses
- −curl | bash install pattern is a security risk
- −Limited differentiation
Verdict
Decent option if you want crypto payments or global datacenter choice. The curl-pipe-bash install is a red flag for security-conscious users.