ClawDeploy
LiveOne-click OpenClaw deployment for non-technical users with multi-model support
Security Score: 3.9/100 — Basic
ClawDeploy is a very early-stage OpenClaw hosting provider that launched in early 2026. The product focuses almost entirely on ease of deployment for non-technical users ('one-click provisioning'). The GitHub org shows just 16 total contributions, 2 contributors, and repos created in February 2026. There is no documentation, no security page, no blog, and no about page. The privacy policy and terms of service are minimal but present. The only security-related claim is vague marketing language about 'secure key handling' and 'encrypted secrets.' The related ClawOS project (clawos.xyz) is a separate 'Founderless Startup Factory' concept that appears largely experimental. The extremely limited web presence, absence of any security documentation, and very new GitHub activity pattern suggest this is a pre-maturity product with no meaningful security posture documented.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
The privacy policy states they collect 'encrypted secrets you submit (for example, Telegram bot tokens)' and 'operational data: workflow events, error logs, server IDs, and related diagnostics' but provides no specifics on per-user isolation, encryption at rest, data training exclusions, or log sanitization. No information about cross-agent contamination prevention or employee access controls.
No information found anywhere on the website, docs (none exist), or GitHub about prompt injection prevention, sandboxing, code execution isolation, memory integrity, human-in-the-loop controls, or container escape prevention. The topic of agent hijacking is not addressed at all.
The homepage mentions 'Secure key handling' and 'Keep your bot credentials and provider keys managed in a dedicated authenticated console.' The privacy policy references 'encrypted secrets you submit.' However, no technical details are provided about encryption methods, credential leak detection, log sanitization of secrets, credential rotation, or how credentials are excluded from AI model context. This is marketing language without supporting technical evidence.
No information found about rate limiting, spending caps on agent actions, kill switches, behavioral monitoring, permission scoping, or least-privilege enforcement. The platform provides no documented guardrails against agents sending unauthorized messages or performing unintended actions.
No information found about backups, data export, disaster recovery, data deletion after cancellation, or business continuity. The GitHub presence shows extremely low activity (16 contributions total, repos created Feb 2026, 1 GitHub star, 0 forks, 2 contributors), raising significant concerns about provider longevity. No SLA or uptime commitment is mentioned.
Pricing is clearly published with three tiers: Starter at $24.99/mo with $8 usage allowance, Plus at $45.99/mo with $24 allowance, and Pro at $83.99/mo with $55 allowance. The terms state 'Usage credits or limits may apply by plan' and 'payments are non-refundable.' However, no hard spending caps, overage pricing, or usage alerts are described, and no price change notification policy exists beyond 'We may update these Terms from time to time.'
The privacy policy identifies data processors including 'Neon, Stripe, Hetzner, OpenRouter, Upstash, and authentication providers' and mentions data may be 'processed in countries outside your residence.' However, there is no mention of audit logging, incident response procedures, breach notification timelines, agent action trails, GDPR compliance details, or security monitoring. The terms provide only a generic 'as is' disclaimer.
The privacy policy names third-party processors (Hetzner, OpenRouter, Upstash, Neon, Stripe) and the terms note 'Some functionality depends on third-party services... which may change independently and have their own terms.' No information exists about dependency scanning, MCP server vetting, SBOM, build pipeline integrity, or supply chain security practices. The GitHub repo uses GitHub Actions but no security scanning is evident.
Authentication is Google-only ('Continue with Google' is the sole sign-in option) with no MFA mentioned. The homepage mentions an 'authenticated console' but no details on access control, injection prevention, session management, or TLS configuration. No security page, penetration testing results, or security headers documentation exists. The platform appears very early-stage with minimal security infrastructure.
No information found about hallucination prevention, output verification, approval workflows for high-impact actions, undo/rollback capabilities, or transparency about AI uncertainty. The platform does not address misinformation or trust exploitation risks at all.
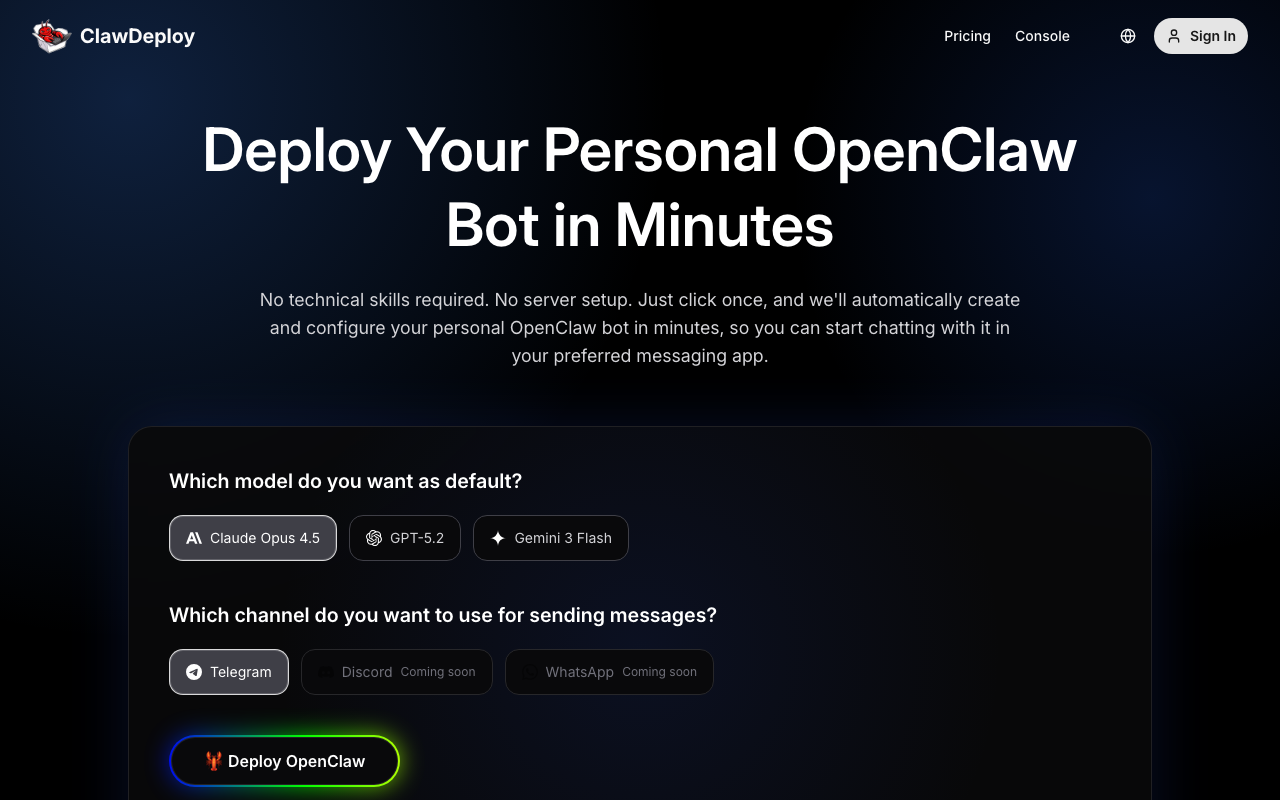
Key Features
- ✓One-click deployment
- ✓Claude Opus 4.5, GPT-5.2, Gemini 3 Flash model choice
- ✓Non-technical user focused
Integrations
Strengths
- +Zero technical knowledge required
- +Multi-model support (Claude, GPT, Gemini)
Weaknesses
- −Telegram-only currently
- −Higher entry price than some competitors ($24.99/mo)
- −New entrant
Verdict
Simple one-click deployment targeting non-technical users. Multi-model choice (Claude, GPT, Gemini) from $24.99/mo. Telegram-only.