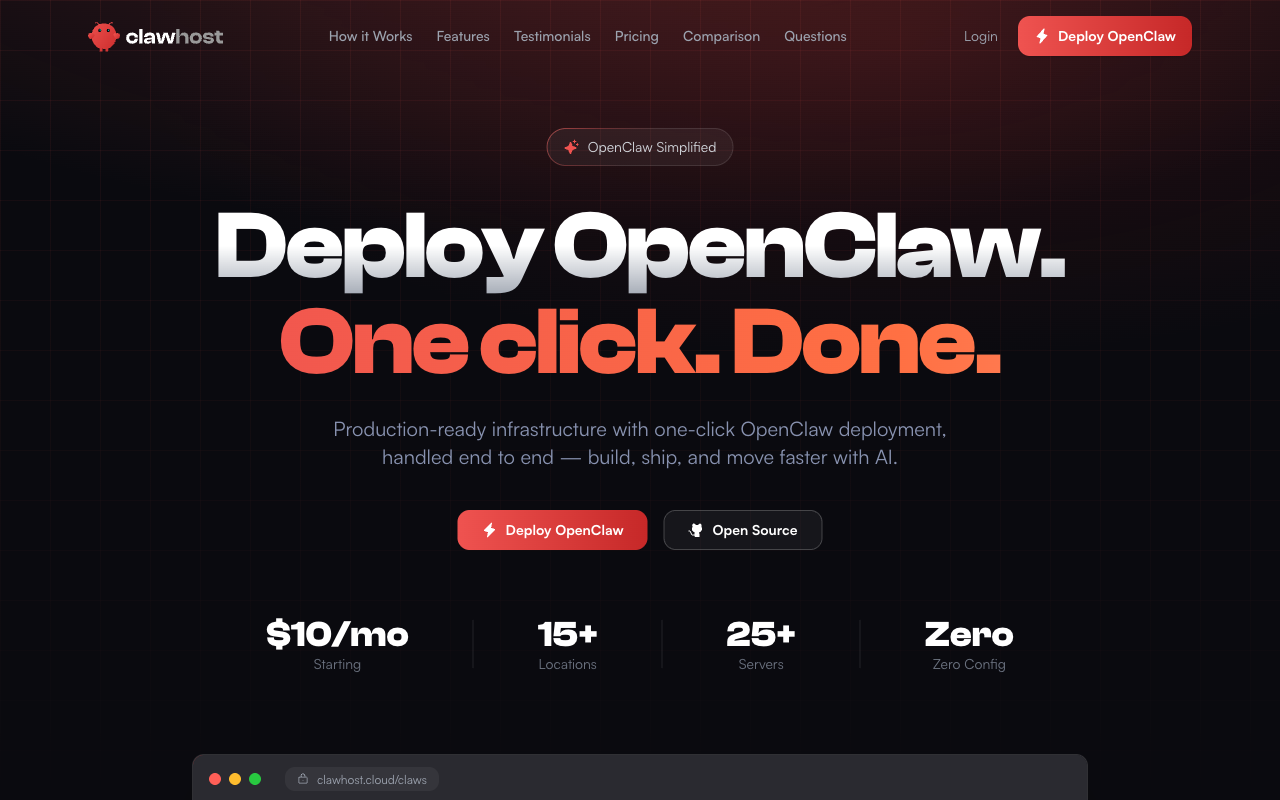
ClawHost Cloud
LiveOpen-source VPS provisioning platform with transparent pricing
Security Score: 7.5/100 — Basic
ClawHost Cloud is a very new platform (Feb 8, 2026) by single developer (bfzli). Core advantage: dedicated-VPS-per-user model provides strong tenant isolation. Fully open source (MIT, 126 GitHub stars). Excellent pricing transparency across 45+ plans. However, no security documentation, no SECURITY.md, no MFA, no backup guarantees. Cloud-init has concerning defaults (allowInsecureAuth:true, HTTP-only Nginx). OpenClaw installed from npm without pinned versions. Extremely early stage with single-developer sustainability risk. More a VPS provisioning tool than a managed security platform.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
Dedicated VPS per user provides strong tenant isolation by architecture. Homepage: '100% Owned Data: Your own server, your data. No shared infrastructure, no logs, no third parties.' Cloud-init shows per-instance gateway auth tokens. However, no encryption-at-rest documentation, no data retention specifics, and no clarity on whether the platform dashboard accesses user agent data.
No documentation on prompt injection defenses, sandboxing, memory integrity, or human-in-the-loop. Platform deploys vanilla OpenClaw on VPS. Cloud-init sets 'allowInsecureAuth: true' on the gateway — a red flag that could expose agent management to unauthorized access. No container isolation or code execution sandboxing.
Architecture means credentials live on user's own VPS (not stored centrally by ClawHost) — positive. But no secrets management, root passwords injected via cloud-init template, gateway tokens stored in plaintext JSON on disk. No credential rotation, leak detection, or encryption of credentials at rest documented.
Zero guardrails, rate limiting, behavioral monitoring, or kill switch for individual agents. Instance-level start/stop/restart exist but no agent-level controls. Platform provides raw VPS with OpenClaw installed — no platform-level rogue agent prevention.
Recently added 'Export your OpenClaw as a portable zip archive' (Feb 14 changelog). Platform fully open source (MIT) — no vendor lock-in. However, no backup policy, no SLA, Terms allow discontinuation 'with or without notice.' Launched Feb 8, 2026 by single developer — significant bus factor risk.
Pricing transparent: 45+ server plans across Hetzner/DigitalOcean/Vultr with exact specs and monthly costs. '$10/mo Starting.' Terms: 'Services are billed on a fixed monthly basis.' 'Cancel anytime.' No hidden fees — users pay only server cost. However, no spending caps or usage alerts. 'Prices subject to change with reasonable notice.'
No SECURITY.md on GitHub, no security advisories, no incident response, no audit logging, no breach notification, no compliance certifications. Privacy Policy generic: 'appropriate technical and organizational measures.' Terms allow modification 'with or without notice.' No GDPR DPA. Single developer with no organizational accountability.
GitHub reveals full stack: Firebase auth, Hetzner/DO/Vultr APIs, Cloudflare DNS, Polar.sh billing. Cloud-init installs OpenClaw from npm ('npm install -g openclaw@latest') without pinned versions or integrity checks. No SBOM, no dependency scanning. Latest CI build shows failure. Auto-updates claimed but mechanism undocumented.
Firebase magic link + Google/GitHub OAuth — reasonable but no MFA. Cloud-init sets 'allowInsecureAuth: true.' UFW configured (22/80/443), gateway binds to loopback only. But Nginx config only HTTP (port 80) — SSL via Let's Encrypt mentioned in README but absent from cloud-init template. No security testing, no rate limiting documented.
No documentation on hallucination mitigation, output verification, approval workflows, or AI uncertainty. Platform deploys vanilla OpenClaw without additional trust layers.
Key Features
- ✓Open-source platform (MIT license)
- ✓30+ global locations
- ✓45+ server configurations
- ✓Zero-config deployment
- ✓Full SSH access
- ✓Multiple VPS providers
Strengths
- +Open-source — inspect the code yourself
- +Wide range of server sizes
- +Transparent infrastructure pricing
- +Full root/SSH access
Weaknesses
- −No messaging integrations listed on site
- −Security is your responsibility
- −Requires some technical knowledge
- −New entrant, limited track record
Verdict
Good open-source option if you want transparency and full control. Wide server range from $10 to $350/mo, but no messaging integrations visible.