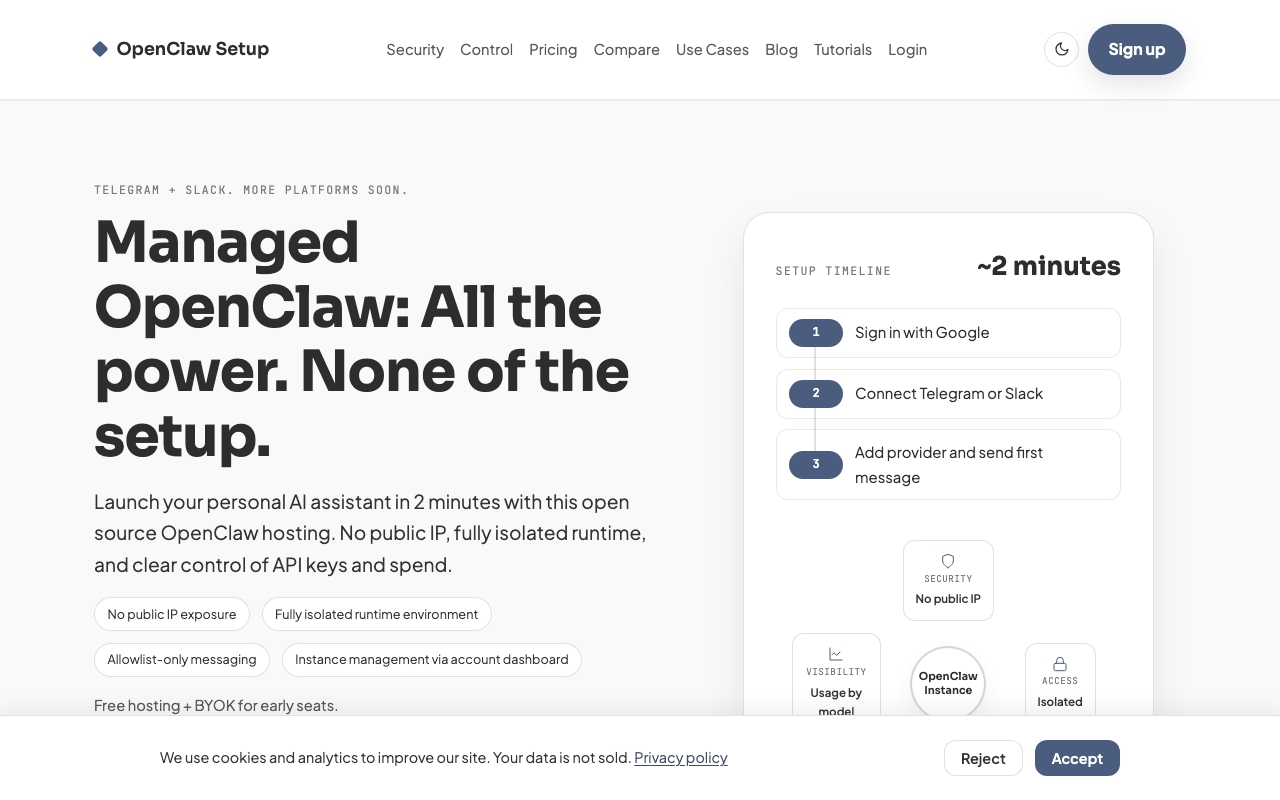
OpenClaw Setup
LivePrivacy-focused managed hosting with full cost transparency and key separation
Security Score: 27.9/100 — Good
OpenClaw Setup is a solo-operated managed hosting provider (Gregory Potemkin / Lemon AI LLC, Wyoming) for the open-source OpenClaw AI agent framework. Its strongest area is credential security, with documented AES-256-GCM encryption and key isolation from agent runtime. Infrastructure isolation via Kubernetes pods with NetworkPolicy is well-documented in the security blog post. However, the provider has significant gaps: no incident response process, no audit logging, no guardrails against agent misbehavior (agents run with full root capability), no MFA beyond what Google provides, and minimal accountability infrastructure. The single-operator nature raises durability concerns. The security blog post is unusually detailed and transparent about upstream OpenClaw risks (41 CVEs, plaintext credential storage in self-hosted version), which demonstrates genuine security awareness — but many claims about the managed platform's security architecture are documented only in blog content, not in a dedicated security page or verifiable audit. Currently free with BYOK model; future pricing is undefined.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
Provider documents specific isolation measures: 'your assistant runs separately from other users and internal services' with Kubernetes pod isolation and NetworkPolicy enforcement blocking pod-to-pod communication. Privacy policy states 'we do not store LLM request or response content in our platform database' and 'we do not store sensitive data from your conversations.' Employee access is consent-gated: 'Support can access your account or instance only upon your explicit request or permission.' However, there is no mention of data not being used for AI training (though BYOK means data goes directly to the user's own LLM provider), and log sanitization details are minimal — logs are stored 'on the machine running the pod' with 'default Kubernetes retention.'
Provider documents allowlist-only access control: 'every OpenClaw Setup instance launches with dmPolicy: "allowlist" and groupPolicy: "allowlist"' with unknown senders 'silently ignored.' No public IP exposure reduces attack surface: 'your assistant is not exposed to direct public-IP probing or scanning.' Kubernetes pod isolation with 'no pod-to-pod communication, no access to the Kubernetes API, cluster services, or cloud metadata endpoints' and egress limited to 'public internet on ports 80/443, with all private IP ranges blocked.' However, there is no documented prompt injection defense, memory integrity protection, or human-in-the-loop approval for code execution — the agent runs with 'full root-level capability.'
This is the provider's strongest documented area. Credentials are encrypted with 'AES-256-GCM before being stored in the database' with 'the encryption master key is a Kubernetes Secret in the platform namespace, inaccessible to user pods.' Key isolation is specifically addressed: 'credentials accessed via proxy; your agent never sees raw API keys' and 'decrypted only at provision/restart and written to auth-profiles.json inside the pod — never to environment variables.' Privacy policy confirms 'AES-256-GCM for credentials and sensitive data.' No mention of credential rotation, leak detection in outputs, or credential lifecycle management, which are gaps.
Very limited guardrails documented. The provider mentions 'cost control: see token usage by model and time to catch surprises early' for visibility, and resource limits are enforced per pod ('500m CPU, 512Mi RAM, 20Gi storage'). However, there is no documented emergency kill switch, no human-in-the-loop for high-risk actions, no rate limiting on messaging, no tool classification or gating, and agents explicitly have 'full root-level capability to run code, install packages, and execute workflows.' The terms place all responsibility on the user: 'You are responsible for... actions your agent takes.'
Provider mentions data export: 'You can export your workspace and configuration at any time from the dashboard. Secrets are excluded or redacted.' FAQ confirms 'workspace export is available anytime.' However, there is no mention of backups, disaster recovery, uptime SLAs, or what happens if the provider shuts down. Terms state the service is 'as is' with no warranty of 'uninterrupted or error-free operation.' The provider is a single-person operation (Gregory Potemkin) through Lemon AI LLC — a Wyoming registered agent address, which raises provider stability concerns. No circuit breakers or blast-radius limits are documented.
BYOK model is transparent: 'You provide your own LLM provider credentials... You are responsible for all costs billed by your LLM provider. We do not markup or resell LLM usage.' Dashboard provides 'token and cost analytics by model and time' with per-model cost breakdowns visible in the UI. However, there are no documented hard spending caps, no usage alerts or notifications, and no price change notification policy. The free tier has no stated limits beyond resource caps (500m CPU, 512Mi RAM), and 'managed keys coming soon' suggests future paid tiers with undefined pricing.
Limited accountability infrastructure. Privacy policy states the company is 'Lemon AI LLC' in Wyoming with a contact email. Terms specify 'laws of the State of Wyoming' for governing law. Support access requires 'explicit request or permission.' However, there is no documented incident response process, no breach notification timeline, no audit logging of agent actions, no compliance certifications (GDPR, SOC 2), and no security monitoring is described. Logs are mentioned only as stored on the pod machine with 'default Kubernetes retention' and only the operator has access.
The security blog post demonstrates awareness of upstream OpenClaw risks: '41 CVEs and counting' with detailed vulnerability tracking. Provider handles managed updates: 'security patches and OpenClaw version updates are applied across all instances.' The blog documents the plugin supply chain risk: 'OpenClaw's plugin system runs third-party code without sandboxing' but does not clarify how the managed platform mitigates this for hosted instances. No SBOM, no dependency scanning details, no build pipeline integrity measures are documented. No mention of how MCP servers or third-party tools are vetted.
Authentication is Google OAuth only — no native MFA option, but Google accounts can have 2FA enabled. Session management uses 'JWT in HTTP-only cookie.' Kubernetes infrastructure includes 'allowPrivilegeEscalation: false,' seccomp default profile, no service account token mounted, and NetworkPolicy enforcement. TLS is used (HTTPS observed on all pages). However, there is no mention of independent security testing, penetration testing, or bug bounty program. No SSRF protection documented for the platform itself (only for the upstream OpenClaw project). No inter-agent communication security documented despite supporting multiple instances.
No information found on this topic. There are no documented approval workflows, no independent verification for high-impact decisions, no output manipulation monitoring, no undo/rollback capability, and no transparency about AI uncertainty. The provider positions itself as infrastructure ('we provide the platform') and does not address the trust and misinformation risks inherent in autonomous AI agents.
Key Features
- ✓Managed hosting for OpenClaw + Telegram
- ✓Full cost transparency (usage by model and time)
- ✓API key separation from agent
- ✓Security-by-design
- ✓No server management required
Integrations
Strengths
- +Strong emphasis on cost transparency
- +API key separation is a real security feature
- +Privacy-conscious positioning
Weaknesses
- −Free tier limited to first 50 seats
- −Telegram-only integration
- −New entrant, limited details available
Verdict
Privacy-focused option with free BYOK hosting (first 50 seats). The API key separation is a real differentiator for security-conscious users.