RunClaw.ai
BetaBest BudgetBudget managed hosting with dedicated VMs and EU-based infrastructure
Security Score: 25.8/100 — Good
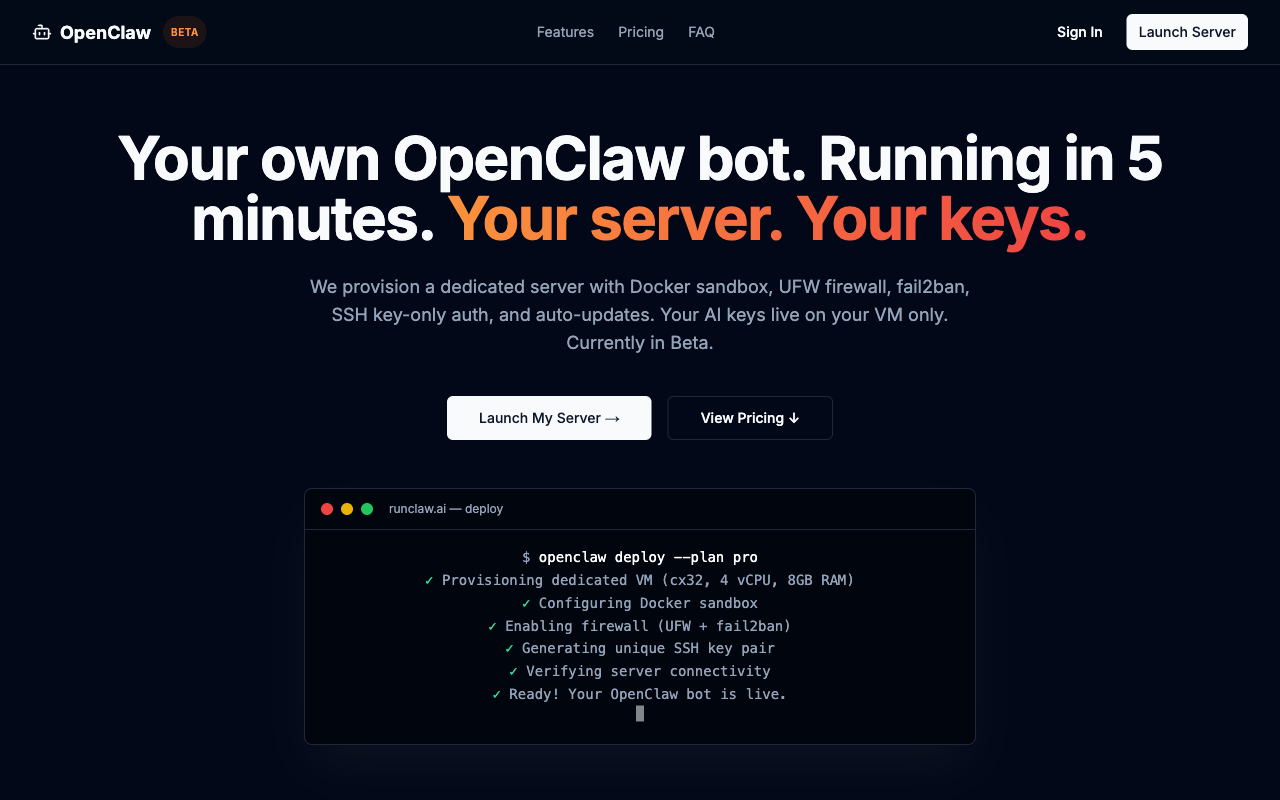
RunClaw.ai is a beta-stage managed OpenClaw hosting provider with dedicated Hetzner VMs in Germany and solid infrastructure security (Docker sandbox, UFW, fail2ban, SSH key-only auth, AES-256 key encryption). The dedicated VM model avoids multi-tenancy risks. BYOK keeps API keys on user VMs. However, the bot runs with root access by design with no documented guardrails. Authentication via Clerk is solid but MFA not required. Upstream OpenClaw has extensive security features but RunClaw doesn't document which they enable by default. Infrastructure security is well-specified with named technologies; application-level agent safety and accountability are largely undocumented.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
RunClaw provides dedicated per-user VMs on Hetzner, giving strong per-user isolation (no multi-tenancy). They claim 'Your API keys, conversations, and all data live exclusively on your dedicated VM. We never access, store, or log your conversations.' SSH keys are 'unique per-instance ed25519 keys encrypted at rest with AES-256.' However, no mention of data-not-used-for-training policy, no log sanitization, no documented employee access controls. The provider holds an encrypted SSH key copy, which is a trust point.
RunClaw deploys OpenClaw inside a Docker sandbox: 'Every server runs Docker-sandboxed with UFW firewall, fail2ban brute-force protection, and SSH key-only auth.' However, 'The bot runs with root access on your dedicated VM. This means it can install packages, modify system files, open network ports, and run any command. This is by design.' No mention of prompt injection defenses, memory integrity protection, or output sanitization specific to RunClaw's setup.
BYOK model: 'You provide your own Anthropic, OpenAI, or other LLM API key. It is stored only on your VM and never touches our systems.' SSH keys use 'unique per-instance ed25519 keys encrypted at rest with AES-256' and the terminal key is 'decrypted in memory only during the session.' However, no credential leak detection, no rotation mechanisms, no documentation on whether credentials are excluded from AI model context.
RunClaw explicitly states: 'The bot runs with root access...This is by design — it needs root to be fully useful. You are responsible for what you instruct the bot to do.' No kill switches, rate limits, behavioral monitoring, or high-risk tool gating documented. The Docker sandbox provides container-level isolation but 'the bot itself operates at the system level.'
All plans include daily backups. 'Your instance will remain active for a 7-day grace period so you can export any data. After the grace period, the VM and all associated data are securely destroyed.' Users can SSH directly and export. Terms mention 30-day grace period. However, no tested restore procedures, no circuit breakers, no SLA. Beta service currently at capacity with waitlist.
Pricing transparent: plans at $13/$15/$19 per month showing 'Hetzner CX33 €5.49/mo + $9 managed service.' Terms state '30 days' notice' for price changes. BYOK means users control API spending separately. However, root access bot can open ports potentially causing unexpected bandwidth costs.
Privacy Policy mentions standard data rights and '30 days' for data deletion. VMs hosted in Hetzner Germany (EU). Security measures listed: 'encryption in transit (TLS), Docker sandboxing, UFW firewall rules, and fail2ban intrusion prevention.' No audit logging, incident response process, breach notification timeline, or agent action audit trail documented.
Hosts open-source OpenClaw (MIT, 201k GitHub stars). 'We test new releases in a staging environment first. Once verified, updates are deployed to your instance automatically with zero downtime. If an update causes issues, we roll back immediately.' However, no dependency scanning, SBOM, MCP server vetting, or build pipeline integrity documentation.
Authentication via Clerk (GitHub, Google, email/password). Infrastructure: 'UFW firewall (all inbound denied except SSH on port 22), fail2ban (bans IPs after 5 failed login attempts), SSH key-only authentication.' Web terminal 'HTTPS WebSocket connection to our backend, which then bridges to SSH on your VM using your instance's encrypted key.' However, MFA not documented as required, no penetration testing or independent security testing mentioned.
No information found about hallucination mitigation, approval workflows, output verification, undo/rollback, or AI uncertainty transparency.
Key Features
- ✓5-minute deployment
- ✓Full SSH access
- ✓Auto-updates with rollback
- ✓EU-based hosting (Hetzner Germany)
- ✓Web terminal
- ✓Daily backups
Integrations
Strengths
- +Cheapest managed hosting with dedicated VMs
- +Full SSH/root access
- +Transparent pricing breakdown
- +EU data residency (GDPR-friendly)
Weaknesses
- −Still in beta
- −No social proof yet
- −EU-only (geographic limitation)
Verdict
Best budget option with real VM isolation. Great for EU-based users who want SSH access and transparent pricing.