agent37.com
LiveUltra-cheap hosting via high-density containers
Security Score: 6.2/100 — Basic
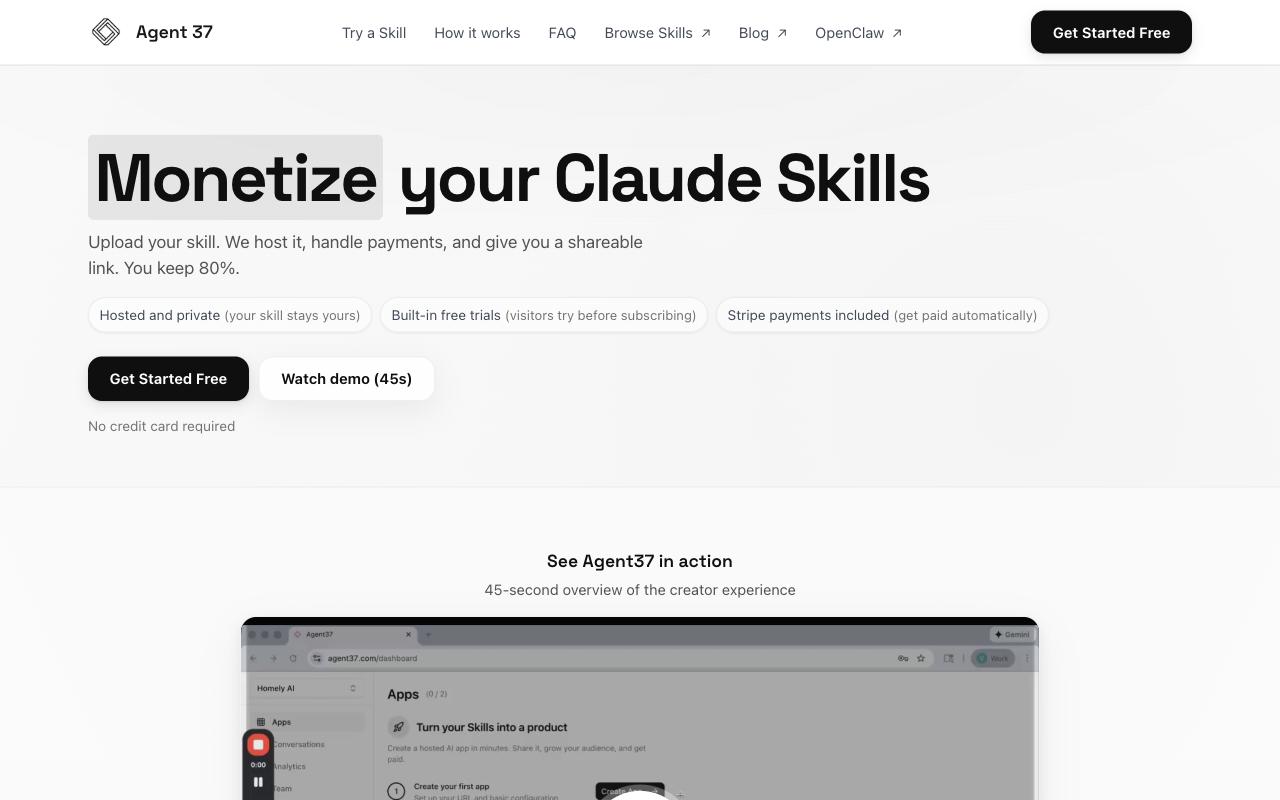
Agent37 is a very early-stage OpenClaw hosting provider (founded 2025, based in New York) offering low-cost managed container hosting at $3.99/mo. The platform's primary focus is accessibility and low friction ('live in ~30 seconds') rather than security. While it claims Docker container isolation and industry-standard encryption, virtually no technical security details are documented. There is no dedicated security page (404), no docs page (404), no GitHub repo for their infrastructure, no third-party audits, no compliance certifications, and no documented incident response process. The privacy policy notably states data may be used to improve AI models. The AI Safety page is focused on content moderation and child safety for their voice-AI coaching product rather than infrastructure security for OpenClaw hosting. The terms of service include broad liability limitations and reserve the right to modify or discontinue service without notice. For a platform where users hand over API keys and run autonomous agents with full shell access, the lack of documented security practices is a significant concern.
10 risk categories scored 1-10 × evidence weight. Based on our methodology, grounded in OWASP Agentic Security, NIST CSF 2.0, and CIS Controls.
The homepage FAQ states 'Each instance runs in its own Docker container with dedicated resources, separate storage, and network isolation.' The privacy policy mentions 'industry-standard encryption and security measures' and 'individual secure environments with unique identifiers.' However, no specifics are given on encryption type, key management, or employee access controls. Critically, the privacy policy states data is used to 'improve our AI models and platform functionality,' suggesting conversation data may be used for training. No data retention policy is documented.
No information found on prompt injection defenses, sandboxing specifics beyond 'Docker container,' memory integrity protection, human-in-the-loop approvals, or container escape prevention. The OpenClaw page mentions 'full shell access (TTYD)' which implies broad permissions but no documentation on how code execution is sandboxed or how cross-container attacks are prevented.
No information found on how user API keys, bot tokens, or other credentials are stored. No mention of encrypted credential storage, credential rotation, leak detection in outputs, or least-privilege access patterns. The platform offers 'full shell access' which raises questions about credential visibility in the environment, but no mitigations are documented.
No information found on rate limiting, spending caps on agent actions, kill switches, behavioral monitoring, least-privilege tooling, or human-in-the-loop approval for high-risk actions. The platform provides OpenClaw with full shell access but documents no guardrails against runaway agent behavior.
The FAQ states 'You can export your data before cancelling' and 'Your instance stops at the end of the billing period.' However, no backup procedures, restore capabilities, uptime SLAs, or data lifecycle policies are documented. The terms state they can 'modify or discontinue, temporarily or permanently, the service with or without notice,' providing no stability guarantees.
Pricing is clearly documented: $3.99/mo early adopter (63 of 500 spots left), then $9.99/mo for new signups. Specs are transparent: '2 vCPU + 4 GB RAM reserved (burst to 6 GB cap).' FAQ states 'No hidden fees, no penalty' for cancellation. However, no hard spending caps on API usage are mentioned, no usage alerts, and terms allow pricing changes with only a date update notification.
The safety page mentions 'audit logs of conversations' and enterprise 'comprehensive conversation logs (privacy-respecting) for compliance and quality assurance.' The safety page also mentions content reporting mechanisms. However, no incident response process is documented, no breach notification timeline, no data jurisdiction disclosure (footer says 'Made with love in New York' but no formal jurisdiction statement), and 'regular audits' are specified as 'internal reviews' only.
The safety page identifies Google Gemini as the primary AI model and mentions adherence to 'acceptable use policies of Google Gemini.' No information on dependency scanning, MCP server vetting, SBOM, build pipeline integrity, or patching cadence. The skills marketplace indexes from public GitHub repositories but no vetting process is described for hosted skills.
SSL/HTTPS is confirmed as 'included' for instances. Docker container isolation is claimed. No information on MFA, authentication strength, SSRF protection, injection prevention, security hardening, or independent security testing. No dedicated /security page exists (returns 404). The platform provides TTYD shell access but does not document how the web terminal is secured.
The safety page has a detailed 'AI Limitations & Disclaimers' section stating 'AI agents may occasionally produce inaccurate or incomplete information' and 'AI-generated responses should not be considered professional advice.' Content moderation with 'input filtering' and 'output filtering' is claimed. The safety page mentions 'measures to reduce the generation of false or misleading information.' However, no specific approval workflows, undo capabilities, or independent verification mechanisms are documented.
Key Features
- ✓30-second setup
- ✓No config required
- ✓Full UI and terminal access
- ✓SSL included
- ✓Burst capacity (6GB)
Strengths
- +Absolute lowest price
- +Minimal friction setup
- +Full UI and terminal access included
Weaknesses
- −Likely resource-oversubscribed
- −Reliability questioned by HN community
- −No backups or persistence mentioned
- −Container isolation only (weakest)
- −Already raised prices once
Verdict
Cheapest option for experimenting, but you get what you pay for. Bare-bones features at rock-bottom price.